April 6, 2026
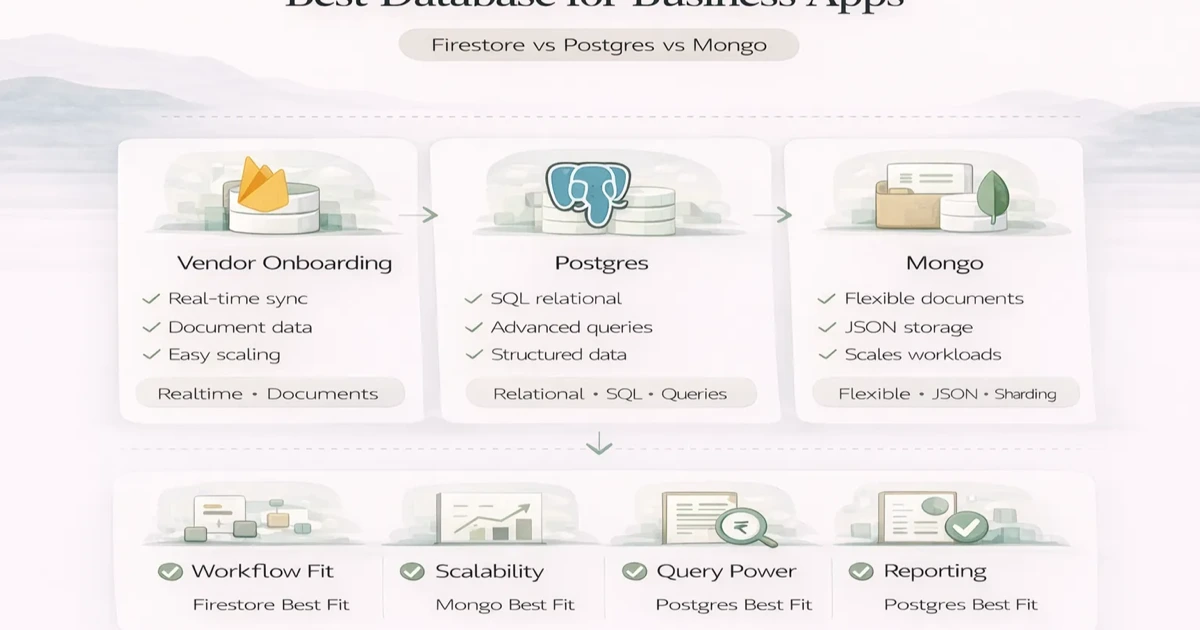
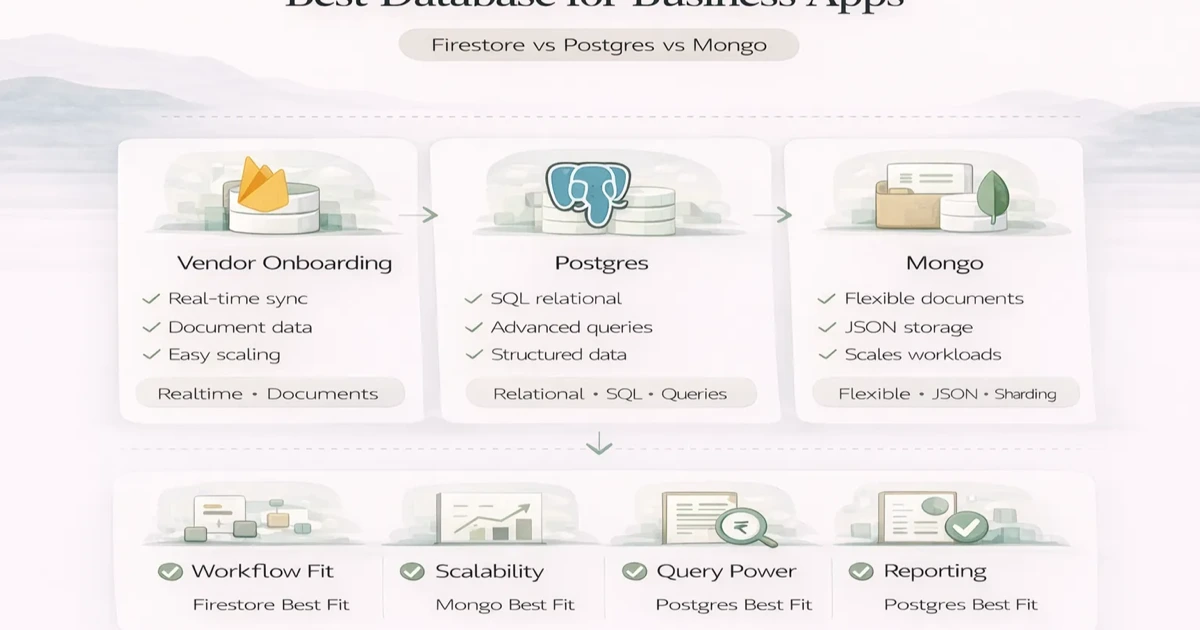
Best Database for Business Apps: Firestore vs Postgres vs Mongo
Best database for business apps: Firestore vs Postgres vs Mongo explained for data models, scaling, workflow fit, and long-term app needs in 2026.
Read articleApril 6, 2026
Security for web apps guide with role-based access best practices, common mistakes, and safer implementation advice for business apps in 2026.

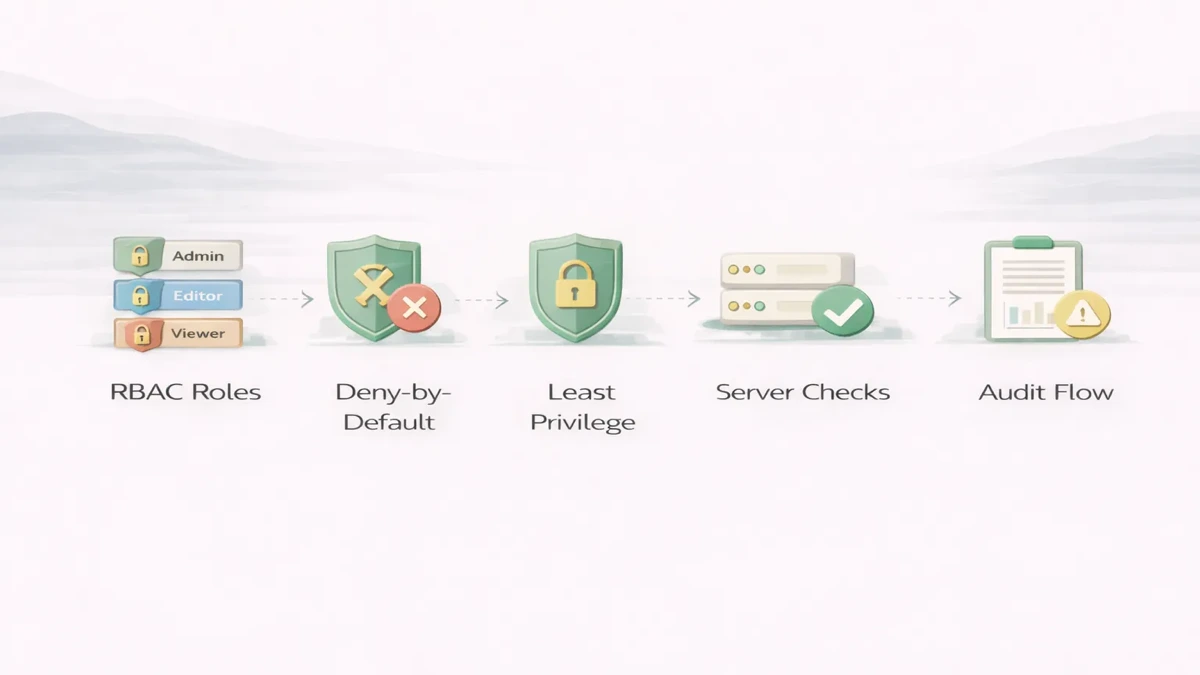
Access control is one of the most common failure points in business apps. Teams spend time on login, UI polish, workflows, and reports, but role rules remain weak or inconsistent. That creates problems quickly: users seeing data they should not see, actions happening without proper authorization, and internal trust in the system going down.
Role-based access control, or RBAC, helps organize permissions around defined roles. But RBAC only improves security if it is implemented carefully. A weak role model, UI-only checks, or unclear permission design can create risk even when the app looks secure on the surface.
This guide explains practical RBAC best practices for web apps, what common mistakes to avoid, and how to build safer access control into business software.

Good RBAC means:
The safest practical rules are:
RBAC should make the system safer and simpler to reason about, not more confusing.
For many business apps, access control applies to:
Typical roles:
The exact roles should come from actual business workflow, not random labels.
If a route, record, or action is sensitive, the safe default is no access unless it is explicitly allowed.
Give users only the permissions required for their actual job.
Never rely only on hiding buttons in the frontend. The backend must verify access on every protected request.
Do not bundle too many powers into one role. For example:
These should often be separate permissions.
Approvals, exports, deletions, and permission changes should have logs.
If the button is hidden but the API still accepts the request, the app is not secure.
Sometimes teams make one wide role that can do almost everything. That simplifies development in the short term but increases risk.
Some actions depend not just on role, but on ownership or department scope.
RBAC should be reviewed when workflows change. Otherwise old permissions stay wider than needed.
Stronger access control affects scope in useful ways:
Typical implementation cost impact:
₹20,000 to ₹60,000₹60,000 to ₹2 lakh₹2 lakh+Timeline depends on:
Role-based access control should protect actions, data, reports, and admin settings. A secure web app should not only hide menu items; the backend must enforce permissions too.
Before launch, define:
RBAC should be scoped during web application services or software development, not added casually at the end.
If your web app has approvals, reports, exports, or sensitive records, do not treat RBAC as a finishing task. Access control design affects the backend, data model, and workflow quality from the beginning.
Not always. Some apps also need ownership-based or attribute-based rules, but RBAC is often the right starting layer.
Yes. Frontend helps UX, backend enforces real security.
Deny by default and grant only what is necessary.
Yes. Exporting data can be a sensitive action.
For approvals, admin changes, and high-risk actions, yes.
Sometimes, but in larger apps even admin functions may need separation.
Relying on UI hiding instead of server-side enforcement.
At architecture and workflow design stage, not only at the end.
If you want role-based access that supports approvals, reporting, and sensitive operations safely, define the permission matrix and protected actions before the backend grows around weak assumptions.
Related Articles
April 6, 2026
Best database for business apps: Firestore vs Postgres vs Mongo explained for data models, scaling, workflow fit, and long-term app needs in 2026.
Read article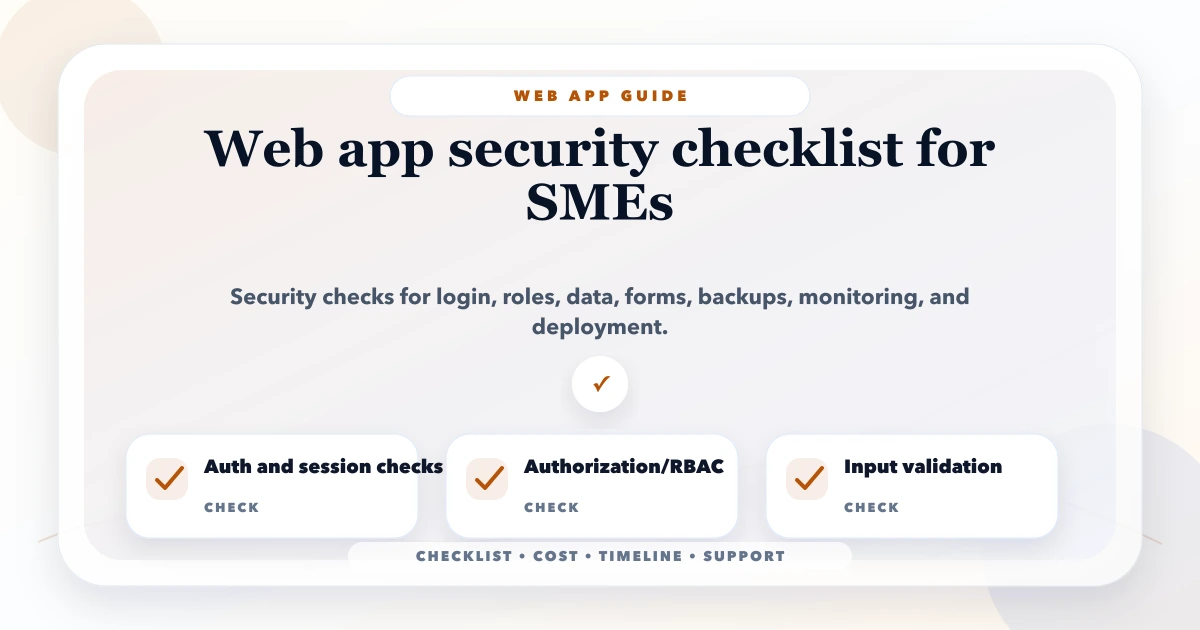
May 17, 2026
web app security checklist for SMEs: practical 2026 guide with checklist, cost, roadmap, tools, mistakes, FAQs, and next steps for Indian SMBs today safely.
Read article
May 3, 2026
Mobile App Development Company in Delhi NCR (2026) guide with pricing, process, timeline, deliverables, proof links, and practical planning for businesses.
Read article